Vectra NDR
How can a network-centric approach to cybersecurity be implemented?
Threat history is usually in three places: network, endpoint, and logs.
Endpoint Detection and Response (EDR) provides a detailed ground-level view of the processes running on a host and the interactions between them.
Network Detection and Response (NDR) system provides a top view of interactions between all devices on the network.
Security teams then configure Security Information and Event Management (SIEMs) to collect event log information from other systems and correlate data sources.
Security teams using these tools are empowered to answer a wide variety of questions when responding to an incident or looking for threats.
They can answer questions such as: “What did this entity or account do before the warning?”, “What did it do after the warning?” “Can we find out when things started to go bad?”
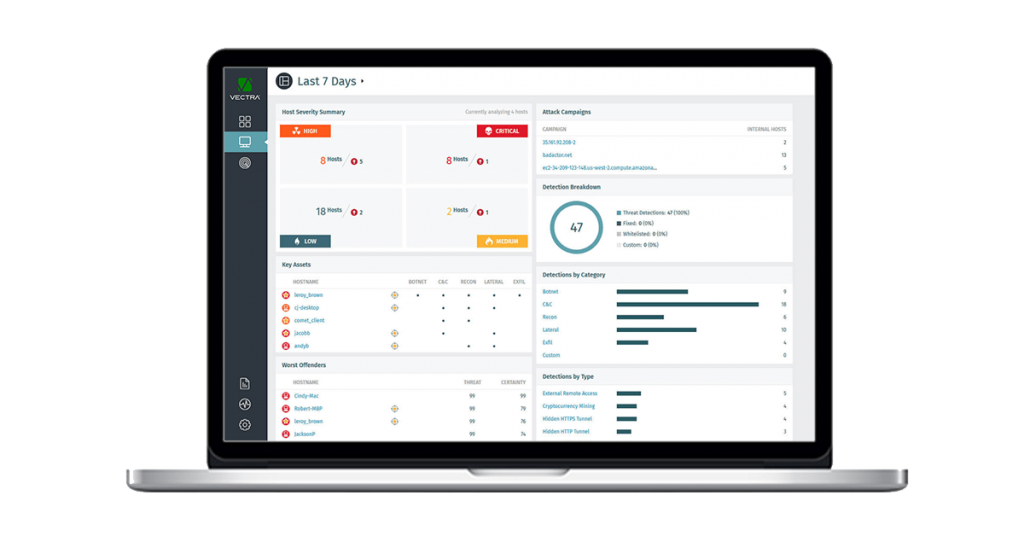
Among this group, NDR is the most critical because it provides a perspective that others cannot.
For example, exploits operating at the BIOS level of a device may corrupt EDR or malicious activity may not be reflected in the logs.
But their activities can be seen by network tools as soon as they interact with any other system through the network.
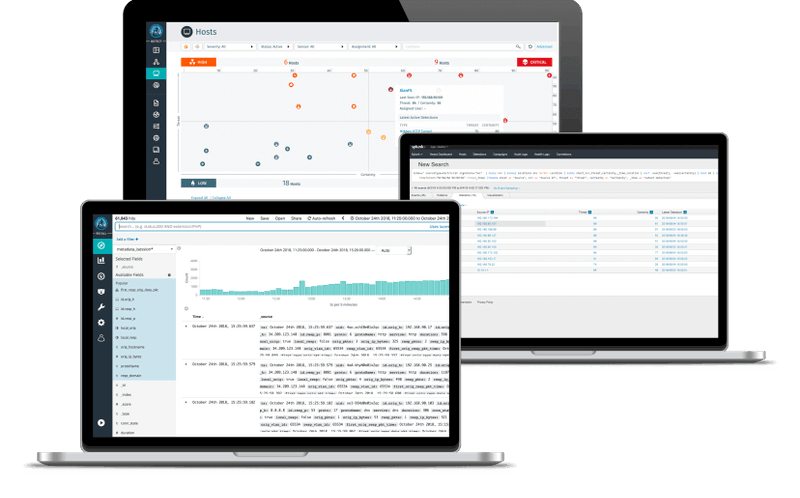
Effective artificial intelligence (AI) based network detection and response platforms collect and store accurate metadata and enrich it with AI-driven security insights.
Effective use of artificial intelligence can then enable real-time detection of attackers and conduct incident investigations.
Powered by artificial intelligence (machine learning, deep learning, and neural networks), aggressive behavior patterns constantly learn and adapt to automatically detect advanced threats in real time before they do harm.
Cyber attack lifecycle:
- Command and control
- Discovery
- Lateral action scenarios
- Data theft
- Botnet networks
NEED MORE INFORMATION?
Didn’t find what you were looking for or need more information or want a quote. Fill out the form on the side and our expert consultants will reach you as soon as possible…















