Another fast-paced maneuver started the day at Cyber World. LimeVPN, a VPN service, was recently hacked, exposing the personal information of thousands of users. Following Facebook and LinkedIn, 69,000 LimeVPN customers’ information is now exposed on the dark web! They are also in the process of selling thousands of user records on the Dark Web and various hacker forums.
What is LimeVPN?
LimeVPN is a low-cost VPN service established in Hong Kong, with servers in the US, UK, Canada, Japan, India, France, Sweden, and other countries. LimeVPN promotes itself as a “affordable VPN provider” with subscription rates starting at $1 per month, as seen right on the homepage.
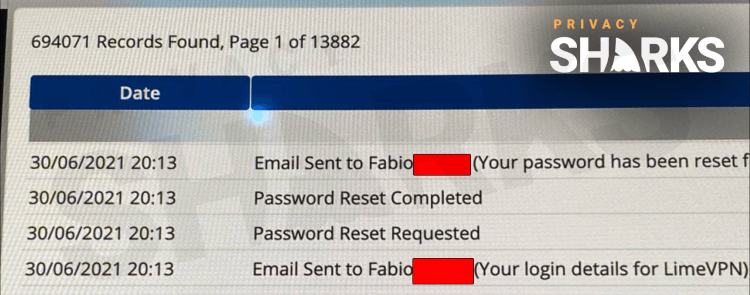
In the screenshot below, you can see that more than 69,000 records were captured and exposed by the hacker:
What does the infiltration contain?
These records include users’ IP addresses, emails, passwords, payment information, and other personal data. You can view the entire thread on this LimeVPN data breach on the RaidForums website.
Hackers gained access to a database of LimeVPN users with passwords and payment information from an unsecured backup server. The infiltration included new data, data from June. Along with accounts and billing information, they stole private keys that can be used to decrypt customers’ VPN traffic. If you look at the screenshots, it turns out that LimeVPN stores a lot of data.
What does the breach mean for LimeVPN?
VPN providers make their money by assuring customers that their data is private and secure with them. In fact, with one security breach, LimeVPN gained the entire database, as opposed to the one. Needless to say, this was a major blow to the company’s image. It will undoubtedly have a strong impact on internet users, hurting their reputation.
LimeVPN’s no-logs policy will also be called into question, as this massive data breach could cause some users to question how much data the company actually stores. Without an independent review of the provider’s privacy policy, the phrase “no records” does not weigh much, and the current situation will cause a lot of scepticism among customers.
These cybersecurity breaches show us once again how important concepts like POPIA, and penetration testing and VPN are.